GUARDING THE GUARDIANS —
Cryptocurrency has repeatedly been prone to theft. Blockchain bridges heighten the hazards.
Dan Goodin –

Getty Photographs
Here’s a story about how a straight ahead instrument bug allowed the fourth-biggest cryptocurrency theft ever.
Hackers stole greater than $323 million in cryptocurrency by exploiting a vulnerability in Wormhole, a Internet-based completely service that permits inter-blockchain transactions. Wormhole lets people switch digital cash tied to 1 blockchain over to a reasonably a couple of blockchain; such blockchain bridges are critically important for decentralized finance (DeFi) corporations and merchandise that function on two or extra chains, on the entire with vastly pretty a couple of protocols, guidelines, and processes.
A guardian with out a enamel
Bridges spend wrapped tokens, which lock tokens in a single blockchain right into a tidy contract. After a decentralized depraved-chain oracle referred to as a “guardian” certifies that the cash include been successfully locked on one chain, the bridge mints or releases tokens of the an an identical worth on the other chain. Wormhole bridges the Solana blockchain with different blockchains, together with these for Avalanche, Oasis, Binance Tidy Chain, Ethereum, Polygon, and Terra.
However what in case you occur to cannot imagine the guardian? A prolonged analysis posted on Twitter a couple of hours after the heist talked about that Wormhole’s backend platform didn’t successfully validate its guardian accounts. By growing a counterfeit guardian fantasy, the hacker or hackers on the help of the heist minted 120,000 ETH cash—worth about $323 million on the time of the transactions—on the Solana chain. The hackers then made a sequence of transfers that dropped about 93,750 tokens into a personal pockets saved on the Ethereum chain, blockchain analysis agency Elliptic talked about.
The hackers pulled off the theft by the utilization of an earlier transaction to make a signatureset, which is a type of credential. With this, they created a VAA, or validator motion approval, which is not any doubt a certificates wished for approving transactions.
“Once they’d the counterfeit ‘signatureset,’ it turned trivial to spend it to generate a positive VAA and set off an unauthorized mint to their very non-public fantasy,” any individual the utilization of the Twitter care for @samczsun wrote. “The consolation is historic earlier. tl;dr—Wormhole didn’t successfully validate all enter accounts, which allowed the attacker to spoof guardian signatures and mint 120,000 ETH on Solana, of which they bridged 93,750 help to Ethereum.”
tl;dr – Wormhole didn’t successfully validate all enter accounts, which allowed the attacker to spoof guardian signatures and mint 120,000 ETH on Solana, of which they bridged 93,750 help to Ethereum.
— samczsun (@samczsun) February 3, 2022
A fluctuate of significant deepdives on the hack are right here and right here.
The haul is the fourth-biggest cryptocurrency theft of all time, in accordance to this roundup from Statista, right on the help of the $480 million stolen from Mt. Gox in 2014, the $547 million taken from Coincheck in 2018, and the $611 million snatched from Polynetwork final twelve months (this document-surroundings amount turned later returned by the thief).
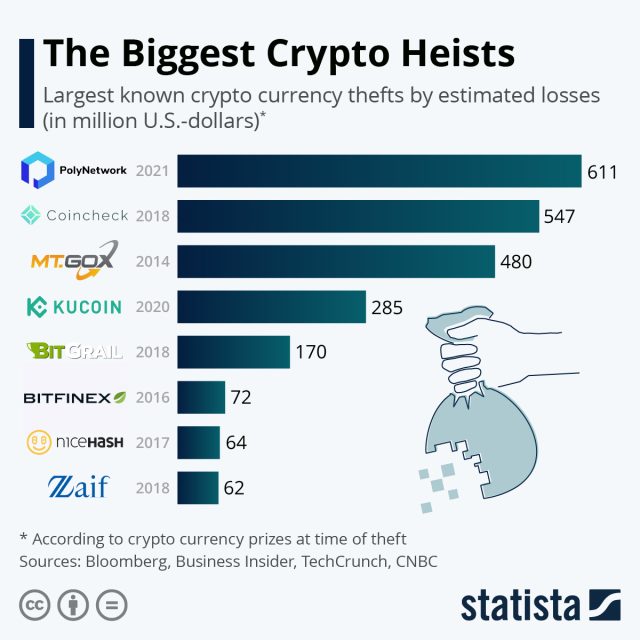
Statista
In 2021, losses from cryptocurrency thefts totaled $10.5 billion, in accordance to Elliptic, up from $1.5 billion the twelve months ahead of.
A nontrivial grief
The Wormhole hack took few blockchain security consultants with out be acutely aware. The grief of writing instrument that interacts with a complete lot of chains in a steady method is nontrivial, and handiest a restricted collection of instruments and ways can check the soundness of the code.
“Constructing bridges inherits the entire complexity of each blockchain,” Dan Guido, CEO of security agency Path of Bits, talked about in a message. “They appear deceptively straight ahead, however they’re amongst probably the most troublesome code to put in writing basically.”
Compounding the grief, the model new hack received right here rapidly after a current exchange turned made in some of the instrument fervent.
“The bridge didn’t quiz that prospects might perchance possibly submit a signatureset, given that exchange to facilitate that turned a current one throughout the Solana runtime,” Guido defined. “By submitting their very non-public signature information, an attacker short-circuited a signature check that allowed them to buy possession of a honorable amount of tokens.”
In an electronic mail, Dane Sherret, a decisions architect at bug-reporting service HackerOne, defined it this vogue:
There’s a
verify_signaturestrustworthy that’s speculated to buy cryptographic signatures from the guardians and bundle them collectively. Regardless of its identify,verify_signaturesdoesn’t in truth check itself—it makes use of thesecp256k1native program on Solana. The mannequin of the solana-program Wormhole turned the utilization of didn’t exactly check the care for, which allowed the hacker to make an fantasy that will perchance possibly bypass the entire assessments.Via the above steps, the hacker turned prepared to bypass the signature assessments and pull the ETH over to Ethereum which supposed that for a time length some of the wETH [the wrapped ETH on Solana] turned not in truth backed by anything.
This hack is arduous for me to wrap my head round because it turned initiated on the Solana blockchain—which makes use of the Rust programming language for its tidy contracts. As Ethereum makes use of the Solidity programming language for its tidy contracts, it’s an instance of how new networks, with pretty a couple of idiosyncrasies and pretty a couple of languages, are in truth speaking to 1 another—which makes security the entire tougher.
Depraved-chain functions pose different dangers as successfully. In a put up penned final month, Ethereum co-founder Vitalik Buterin warned that “conventional security limits of bridges” made them susceptible to a reasonably a couple of class of blockchain exploit recognized as a 51% assault.
Additionally recognized as a majority assault, a 51% assault permits a malicious event that helpful properties greater than 50 p.c of hashing vitality on a blockchain to reverse beforehand made transactions, block new transactions from being confirmed, and exchange the ordering of most fashionable transactions. That opens the door to 1 factor recognized as double spending, a hack that permits the attacker to decide up two or extra funds with the an an identical foreign money tokens. Buterin wrote:
I develop not quiz these issues to bid up straight away. 51% attacking even one chain is troublesome and expensive. Nonetheless, the extra utilization of depraved-chain bridges and apps there could also be, the more severe the problem turns into. No person will 51% assault Ethereum right to buy 100 Solana-WETH (or, for that matter, 51% assault Solana right to buy 100 Ethereum-WSOL). However when there may be 10 million ETH or SOL throughout the bridge, then the inducement to decide up an assault turns into useful larger, and honorable swimming pools might perchance possibly successfully coordinate to decide up the assault occur. So depraved-chain course of has an anti-community create: whereas there is no such thing as a longer useful of it occurring, or not it’s comparatively protected, nevertheless the extra of it’s occurring, the extra the hazards scamper up.
In the meantime, demand for blockchain interoperability continues to develop, seemingly making the safety challenges extra vexing. Every Guido and Sherret urged bridge operators to buy proactive steps to forestall an an identical hacks lastly. Such steps encompass ending a complete lot of security audits and placing handiest restricted efficiency on group allowlists until builders are assured in a trustworthy’s maturity and security.

