FROM RUSSIA WITH MALICE —
Cyberattacks complement and are normally timed to militia actions.
Dan Goodin –
Getty Pictures
On March 1, Russian forces invading Ukraine took out a TV tower in Kyiv after the Kremlin declared its map to destroy “disinformation” inside the neighboring nation. That public act of kinetic destruction accompanied a unparalleled further hidden nevertheless no a lot much less detrimental movement: specializing in a indispensable Ukrainian broadcaster with malware to render its computer systems inoperable.
The dual movement is with out a doubt considered one of many examples of the “hybrid battle” Russia has waged in opposition to Ukraine all by way of the final twelve months, according to a legend revealed Wednesday by Microsoft. Since at the moment sooner than the invasion started, the agency talked about, hackers in six teams aligned with the Kremlin maintain launched no fewer than 237 operations in live performance with the bodily assaults on the battlefield. Virtually 40 of them specializing in a whole lot of strategies weak wiper malware, which deletes invaluable information saved on anxious drives so the machines can’t boot.
“As as we speak’s legend particulars, Russia’s make the most of of cyberattacks seems to be to be strongly correlated and normally right away timed with its kinetic militia operations specializing in merchandise and corporations and establishments invaluable for civilians,” Tom Burt, Microsoft company vice chairman for buyer security, wrote. He talked about the “relentless and damaging Russian cyberattacks” had been specifically relating as a result of a vogue of them targeted critical infrastructure that might maintain cascading detrimental outcomes on the nation.
It’s now not apparent if the Kremlin is coordinating cyber operations with kinetic assaults or in the event that they’re the of independent our our bodies pursuing a stylish function of disrupting or degrading Ukraine’s militia and authorities whereas undermining residents’ perception in these establishments. What’s simple is that the two formulation on this hybrid battle maintain complemented one another.
Examples of Russian cyber actions correlating to political or diplomatic pattern taken in opposition to Ukraine sooner than the invasion started embody:
- The deployment of wiper malware dubbed WhisperGate on a “restricted amount” of Ukrainian authorities and IT sector networks on January 3 and the defacement and DDoSing of Ukrainian web websites a day later. These actions got here as diplomatic talks between Russia and Ukrainian allies broke down.
- DDoS assaults waged on Ukrainian monetary establishments on February 15 and February 16. On February 17, the Kremlin talked about it will probably possibly possibly be “compelled to reply” with militia-technical measures if the US didn’t capitulate to Kremlin calls for.
- The deployment on February 23 of wiper malware by one different Russian converse neighborhood on a whole lot of Ukrainian strategies inside the authorities, IT, vitality, and monetary sectors. Two days earlier, Putin recognized the independence of Ukrainian separatists aligned with Russia.
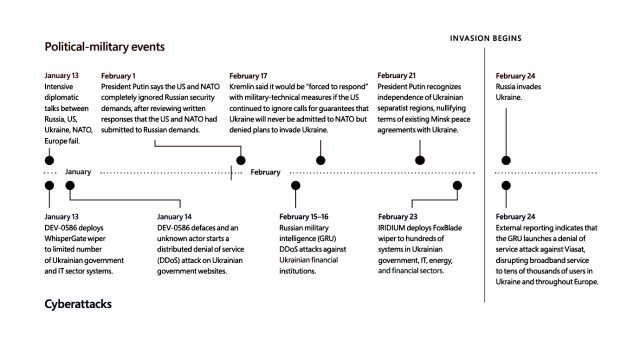
Microsoft
Russia stepped up its cyber offensive as quickly because the invasion started. Highlights embody:
- The February 14 and February 17 compromises of invaluable infrastructure inside the Ukrainian cities of Odesa and Sumy. These actions perceived to carry spot the stage for February 24, when Russian tanks great into Sumy.
- On March 2, Russian hackers burrowed into the community of a Ukrainian nuclear vitality agency. A day later, Russian forces occupied Ukraine’s biggest nuclear vitality spot.
- On March 11, a authorities firm in Dnipro modified into as quickly as targeted with a harmful implant. The identical day, Russian forces launched strikes into Dnipro authorities buildings.
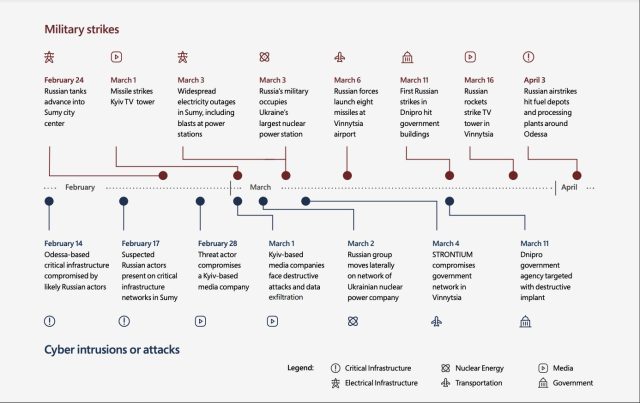
Microsoft
Wednesday’s legend talked about that as early as March 2021, hackers aligned with Russia animated for wrestle with its neighboring nation by escalating actions in opposition to organizations inside or aligned with Ukraine.
The actions haven’t stopped since. Burt wrote:
When Russian troops first started to switch in opposition to the border with Ukraine, we noticed efforts to salvage preliminary entry to targets that might current intelligence on Ukraine’s militia and international partnerships. By mid-2021, Russian actors had been specializing in provide chain distributors in Ukraine and in a international nation to precise further entry now not ultimate to strategies in Ukraine nevertheless additionally NATO member states. In early 2022, when diplomatic efforts didn’t de-escalate mounting tensions round Russia’s militia salvage-up alongside Ukraine’s borders, Russian actors launched damaging wiper malware assaults in opposition to Ukrainian organizations with rising depth. Given that Russian invasion of Ukraine started, Russian cyberattacks have been deployed to pink meat up the militia’s strategic and tactical needs. It’s seemingly the assaults we’ve noticed are ultimate a allotment of job specializing in Ukraine.
The legend entails a variety of security measures that may even be applied by seemingly targets of Russian cyberattacks to protect themselves. One measure entails turning on a attribute referred to as managed folders. The attribute, which isn’t enabled by default, is designed to protect data specifically folders from destruction from ransomware, wipers, and different kinds of damaging malware.

