GOT PATCHES? —
BMCs provide out of the unusual withhold watch over over cloud computer systems. So why hasn’t Quanta patched?
Dan Goodin –
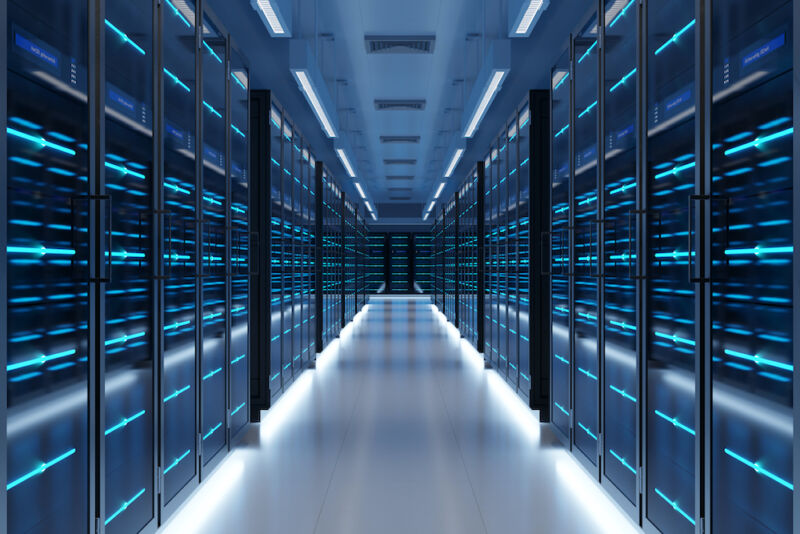
Getty Photographs
In January 2019, a researcher disclosed a devastating vulnerability in one among essentially the most extremely efficient and picked up devices embedded into novel servers and workstations. With a severity rating of 9.8 out of 10, the vulnerability affected a mountainous choice of baseboard administration controllers (BMC) made by a couple of producers. These little computer systems soldered into the motherboard of servers allow cloud facilities, and constantly their clients, to streamline the a ways-off administration of mountainous fleets of computer systems. They allow directors to remotely reinstall OSes, set up and uninstall apps, and withhold watch over nearly about one each different side of the scheme—even when or not it’s grew to show into off.
Pantsdown, as a result of the researcher dubbed the danger, allowed somebody who already had some achieve entry to to the server an out of the unusual alternative. Exploiting the arbitrary learn/write flaw, the hacker might probably presumably even flip appropriate into an enormous admin who often had the simplest degree of withhold watch over for a complete data middle.
The business mobilizes… as antagonistic to for one
Over the following couple of months, a couple of BMC distributors issued patches and advisories that prompt clients why patching the vulnerability grew to become excessive.
Now, researchers from safety company Eclypsium reported a worrying discovering: for causes that stay unanswered, a broadly prone BMC from data middle options supplier Quanta Cloud Know-how, higher acknowledged as QCT, remained unpatched in opposition to the vulnerability as as of late as remaining month.
As if QCT’s comment of being inactive wasn’t ample, the agency’s modern posture additionally stays baffling. After Eclypsium privately reported its findings to QCT, the options agency replied that it had not directly mounted the vulnerability. Nonetheless fairly than submit an advisory and fabricate a patch public—as nearly about every and every agency does when fixing a excessive vulnerability—it prompt Eclypsium it grew to become offering updates privately on a customer-by-customer basis. As this put up grew to become about to jog reside, “CVE-2019-6260,” the business’s designation to trace the vulnerability, did not appear on QCT’s net place.
In an e mail, Eclypsium VP of Know-how John Loucaides wrote:
Eclypsium is persevering with to bag that customized servers (eg. Quanta) stay unpatched to vulnerabilities from as a methods assist as 2019. Proper right here is affecting a myriad of devices from an enormous choice of cloud suppliers. The comment is not at all times in fact somebody vulnerability, or not it’s a methods the scheme that retains cloud servers primitive and prone. Quanta has absolutely simply launched the patch for these strategies, and so they additionally did not present it for verification. Really, their response to us grew to become that it could absolutely be made available upon impact a question to to bolster.”
A pair of Quanta representatives did not reply to 2 emails despatched over consecutive days requesting affirmation of Eclypsium’s timeline and a proof of its patching process and insurance policies.
Latest, however not patched
A weblog put up Eclypsium printed on Thursday shows the type of assault that’s that you could be probably presumably presumably have religion to enact on QCT BMCs the usage of firmware available on QCT’s exchange web page as of ultimate month, greater than three years after Pantsdown got here to mild.
Eclypsium’s accompanying video shows an attacker getting achieve entry to to the BMC after exploiting the vulnerability to change its net server. The attacker then executes a publicly available instrument that makes use of Pantsdown to learn and write to the BMC firmware. The instrument permits the attacker to provide the BMC with code that opens a reverse net shell each time a sound administrator refreshes a webpage or connects to the server. The following time the admin tries to build up both movement, this will fail with a connection error.
On the assist of the scenes, nonetheless, and unbeknownst to the admin, the attacker’s reverse shell opens. From proper right here on, the attacker has fats withhold watch over of the BMC and will probably presumably even finish one factor else with it {that a} sound admin can, together with establishing persevered achieve entry to and even completely bricking the server.
BMC Assault Demo
The power and ease of use of the Pantsdown exploit are by no formulation distinctive. What’s distinctive, opposite to expectations, is that these kinds of assaults enjoyment of remained that you could be probably presumably presumably have religion on BMCs that had been the usage of firmware QCT provided as as of late as remaining month.
QCT’s decision not to submit a patched mannequin of its firmware and even an advisory, coupled with the radio silence with journalists asking genuine questions, might probably presumably even restful be a crimson flag. Information facilities or data middle clients working with this agency’s BMCs might probably presumably even restful confirm their firmware’s integrity or contact QCT’s improve workforce for extra data.
Even when BMCs method from different producers, cloud facilities, and cloud middle clients have to not buy they’re patched in opposition to Pantsdown.
“Proper here’s a excessive comment, and we finish not have religion it’s a methods a diversified incidence,” Loucaides wrote. “Now we enjoyment of thought-about presently deployed devices from every and every OEM that stay prone. Most of these enjoyment of updates that merely weren’t put in. Quanta’s strategies and their response did place them aside, although.”

