SURREPTITIOUS CLICKING AHEAD —
Google eliminates 16 apps after receiving a doc the apps have been committing advert fraud.
Dan Goodin –
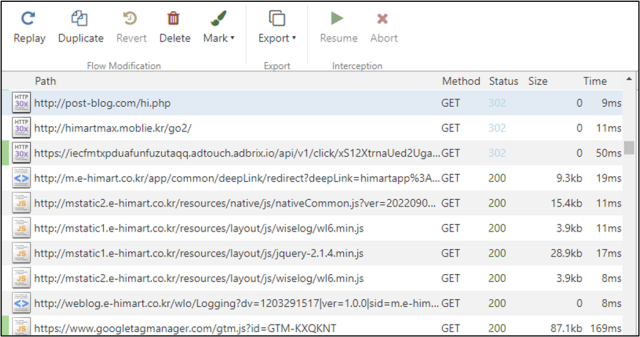
The entire malicious apps obtained right here with a code library named com.liveposting, which acts as an agent and runs hidden spy ware and adware services and products. Assorted apps additionally obtained right here with an extra library referred to as com.click on.cas, which pondering referring to the computerized clicking effectivity. To hide the fallacious habits, the apps waited about an hour after set up ahead of working the libraries.
Advert fraud works via affiliate packages, which permit a 3rd event to obtain a within the discount of of the advert revenue in return for offering hyperlinks that lead discontinue customers to commercials. In would favor to in truth bringing precise customers to the positioning, the fraudsters simulate the referral utilizing bots or different computerized the type to imitate precise person engagement.
The apps detected by McAfee embody:
| Bundle deal title | SHA256 | Identify | Downloaded |
| com.hantor.CozyCamera | a84d51b9d7ae675c38e260b293498db071b1dfb08400b4f65ae51bcda94b253e | Extreme-Flee Digital digital camera | 10,000,000+ |
| com.james.SmartTaskManager | 00c0164d787db2ad6ff4eeebbc0752fcd773e7bf016ea74886da3eeceaefcf76 | Orderly Course of Supervisor | 5,000,000+ |
| kr.caramel.flash_plus | b675404c7e835febe7c6c703b238fb23d67e9bd0df1af0d6d2ff5ddf35923fb3 | Flashlight+ | 1,000,000+ |
| com.smh.memocalendar | 65794d45aa5c486029593a2d12580746582b47f0725f2f002f0f9c4fd1faf92c | 달력메모장 | 1,000,000+ |
| com.joysoft.wordBook | 82723816760f762b18179f3c500c70f210bbad712b0a6dfbfba8d0d77753db8d | Okay-Dictionary | 1,000,000+ |
| com.kmshack.BusanBus | b252f742b8b7ba2fa7a7aa78206271747bcf046817a553e82bd999dc580beabb | BusanBus | 1,000,000+ |
| com.candlencom.candleprotest | a2447364d1338b73a6272ba8028e2524a8f54897ad5495521e4fab9c0fd4df6d | Flashlight+ | 500,000+ |
| com.movinapp.quicknote | a3f484c7aad0c49e50f52d24d3456298e01cd51595c693e0545a7c6c42e460a6 | Fast Show conceal | 500,000+ |
| com.smartwho.SmartCurrencyConverter | a8a744c6aa9443bd5e00f81a504efad3b76841bbb33c40933c2d72423d5da19c | Forex Converter | 500,000+ |
| com.joysoft.barcode | 809752e24aa08f74fce52368c05b082fe2198a291b4c765669b2266105a33c94 | Joycode | 100,000+ |
| com.joysoft.ezdica | 262ad45c077902d603d88d3f6a44fced9905df501e529adc8f57a1358b454040 | EzDica | 100,000+ |
| com.schedulezero.instapp | 1caf0f6ca01dd36ba44c9e53879238cb46ebb525cb91f7e6c34275c4490b86d7 | Instagram Profile Downloader | 100,000+ |
| com.meek.tingboard | 78351c605cfd02e1e5066834755d5a57505ce69ca7d5a1995db5f7d5e47c9da1 | Ez Notes | 100,000+ |
| com.candlencom.flashlite | 4dd39479dd98124fd126d5abac9d0a751bd942b541b4df40cb70088c3f3d49f8 | 손전등 | 1,000+ |
| com.doubleline.calcul | 309db11c2977988a1961f8a8dbfc892cf668d7a4c2b52d45d77862adbb1fd3eb | 계산기 | 100+ |
| com.dev.imagevault | bf1d8ce2deda2e598ee808ded71c3b804704ab6262ab8e2f2e20e6c89c1b3143 | Flashlight+ | 100+ |
In an announcement, a Google spokesperson eminent that each one apps reported by McAfee had been eliminated. The consultant went on to say: “Clients are additionally convey collectively by Google Play Defend, which blocks these apps on Android devices.” The spokesperson didn’t decision a be aware-up quiz asking how the apps racked up 20 million installations within the occasion that they’re blocked.

