CRY, CRY, CRY —
CryWiper masquerades as ransomware, nevertheless its correct plan is to completely assassinate information.
Dan Goodin –
Mayors’ places of work and courts in Russia are under assault by by no methodology-sooner than-viewed malware that poses as ransomware nevertheless is principally a wiper that completely destroys information on an contaminated intention, in line with safety firm Kaspersky and the Izvestia information provider.
Kaspersky researchers agree with named the wiper CryWiper, a nod to the extension .snarl that may get appended to destroyed information. Kaspersky says its workforce has considered the malware beginning “pinpoint assaults” on targets in Russia. Izvestia, in the meantime, reported that the targets are Russian mayors’ places of work and courts. Further main points, alongside facet what variety of organizations have been hit and whether or not or now not the malware effectively wiped information, weren’t immediately recognized.
Wiper malware has grown more and more common over the past decade. In 2012, a wiper is assumed as Shamoon wreaked havoc on Saudi Arabia’s Saudi Aramco and Qatar’s RasGas. 4 years later, a model novel variant of Shamoon returned and struck further than one organizations in Saudi Arabia. In 2017, self-replicating malware dubbed NotPetya unfold at some stage inside the globe in a matter of hours and triggered an estimated $10 billion in injury. Inside the previous 300 and sixty 5 days, a flurry of novel wipers regarded. They encompass DoubleZero, IsaacWiper, HermeticWiper, CaddyWiper, WhisperGate, AcidRain, Industroyer2, and RuRansom.
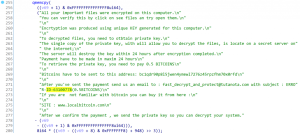
Kaspersky stated it came upon the assault makes an attempt by CryWiper inside the outdated couple of months. After infecting a goal, the malware left a repeat annoying, in line with Izvestia, 0.5 bitcoin and alongside facet a pockets deal with the place the related worth may be made.
Kaspersky
“After analyzing a sample of malware, we got here at some point of out that this Trojan, although it masquerades as a ransomware and extorts money from the sufferer for ‘decrypting’ information, would now not the reality is encrypt, nevertheless purposefully destroys information inside the affected intention,” Kaspersky’s listing stated. “Furthermore, an analysis of the Trojan’s program code confirmed that this was now not a developer’s mistake, nevertheless his distinctive plan.”
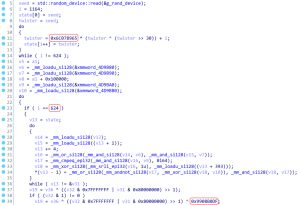
CryWiper bears some resemblance to IsaacWiper, which centered organizations in Ukraine. Every wipers train the the identical algorithm for producing pseudo-random numbers that hotfoot on to dangerous centered information by overwriting the options inside of them. The title of the algorithm is the Mersenne Vortex PRNG. The algorithm is now not frail, so the commonality caught out.
Kaspersky
CryWiper shares a separate commonality with ransomware households is assumed as Trojan-Ransom.Pick32.Xorist and Trojan-Ransom.MSIL.Agent. Significantly, the e-mail deal with inside the ransom repeat of all three is the the identical.
The CryWiper sample Kaspersky analyzed is a 64-bit executable file for Dwelling home windows. It was written in C++ and compiled utilizing the MinGW-w64 toolkit and the GCC compiler. That’s an odd totally different because it’s further common for malware written in C++ to train Microsoft’s Visible Studio. One doubtless explanation for this totally different is that it affords the builders the choice of porting their code to Linux. Given the totally different of express calls CryWiper makes to Dwelling home windows programming interfaces, this plan seems to be unlikely. The additional doubtless plan is that the developer writing the code was utilizing a non-Dwelling home windows instrument.
Profitable wiper assaults on the whole select earnings of sorrowful community safety. Kaspersky suggested community engineers to find out precautions through the use of:
- Behavioral file analysis safety options for endpoint safety.
- Managed detection and response and safety operation coronary heart that allow for well timed detection of an intrusion and select movement to reply.
- Dynamic analysis of mail attachments and blocking of malicious information and URLs. This would possibly effectively effectively effectively earn e mail assaults, considered one of many commonest vectors, further subtle.
- Conducting in mannequin penetration testing and RedTeam duties. This would possibly effectively effectively effectively encourage to title vulnerabilities inside the group’s infrastructure, protect them, and thereby vastly sever the assault floor for intruders.
- Likelihood information monitoring. To detect and block malicious course of in a well timed method, it’s obligatory to agree with up-to-date information in regards to the techniques, devices, and infrastructure of intruders.
Given Russia’s invasion of Ukraine and different geopolitical conflicts raging at some stage inside the globe, the hotfoot of wiper malware isn’t at risk of lifeless inside the upcoming months.
“In a great deal of circumstances, wiper and ransomware incidents are triggered by inadequate community safety, and it’s the strengthening of safety that may agree with to be paid consideration to,” Friday’s Kaspersky listing stated. “We seize that the totally different of cyberattacks, alongside facet these utilizing wipers, will develop, largely attributable to the unstable fear on this planet.”

