BUSTED —
Variston IT fingerprints stumbled on in supply code for developed Chrome exploit.
Dan Goodin –
Google researchers acknowledged on Wednesday they’ve gotten linked a Barcelona, Spain-essentially primarily primarily based solely IT firm to the sale of developed utility frameworks that exploit vulnerabilities in Chrome, Firefox, and Home windows Defender.
Variston IT funds itself as a provider of tailored Recordsdata security options, together with expertise for embedded SCADA (supervisory alter and knowledge acquisition) and Web of Issues integrators, custom-made security patches for proprietary strategies, instruments for knowledge discovery, security teaching, and the enchancment of secure protocols for embedded gadgets. Based solely on a account from Google’s Danger Evaluation Neighborhood, Variston sells each different product not talked about on its internet put of dwelling: utility frameworks that supply everything a buyer must surreptitiously arrange malware on gadgets they’re searching to look on.
Researchers Clement Lecigne and Benoit Sevens acknowledged the exploit frameworks have been at fear of make the most of n-day vulnerabilities, which can greater than seemingly be of us which have been patched at present sufficient that some targets haven’t but put in them. Proof suggests, they added, that the frameworks have been furthermore vulnerable when the vulnerabilities have been zero-days. The researchers are disclosing their findings in an are trying to disrupt the marketplace for spyware and adware, which they acknowledged is booming and poses a risk to a great deal of teams.
“TAG’s take a look at underscores that the commercial surveillance commerce is prospering and has expanded severely in current instances, creating fear for Web prospects throughout the globe,” they wrote. “Industrial spyware and adware places developed surveillance capabilities within the fingers of governments who make the most of them to look on journalists, human rights activists, political opposition, and dissidents.”
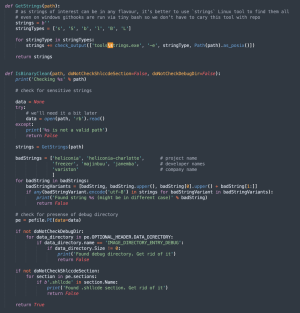
The researchers went on to catalog the frameworks, which they obtained from an nameless supply via Google’s Chrome bug reporting program. Every got here with directions and an archive containing the supply code. The frameworks got here with the names Heliconia Noise, Heliconia Gentle, and Recordsdata. The frameworks contained “extinct supply code in a position to deploying exploits for Chrome, Home windows Defender, and Firefox” respectively.
Built-in within the Heliconia Noise framework turned into code for cleaning up binary information prior to they’re produced by the framework to abolish decided they don’t get pleasure from strings which will per likelihood incriminate the builders. Because the picture of the cleaning script reveals, the guidelines of disagreeable strings integrated “Variston.”
Officers from Variston didn’t reply to an e-mail in search of commentary for this publish.
The frameworks exploited vulnerabilities that Google, Microsoft, and Firefox mounted in 2021 and 2022. Heliconia Noise integrated each an exploit for the Chrome renderer, together with an exploit for escaping the Chrome security sandbox, which is designed to maintain untrusted code contained in a secure environment that may’t protected entry to delicate elements of an working association. Because the vulnerabilities have been stumbled on internally, there do not seem like any CVE designations.
Heliconia Noise might per likelihood very efficiently be configured by the patron to put points benefit from the utmost risk of instances to attend on the exploits, an expiration date, and guidelines specifying when a customer should be considered a sound aim.
Heliconia Gentle integrated a booby-trapped PDF file that exploited CVE-2021-42298, a bug within the JavaScript engine of Microsoft Defender Malware Safety that turned into mounted in November 2021. Merely sending anybody the file turned into sufficient to abolish coveted association privileges on Home windows as a result of Home windows Defender robotically scanned incoming information.
The Recordsdata framework contained an totally documented exploit chain for Firefox working on Home windows and Linux. It exploits CVE-2022-26485, a utilize-after-free vulnerability that Firefox mounted ultimate March. The researchers acknowledged Recordsdata seemingly exploited the code-execution vulnerability since in spite of everything 2019, lengthy prior to it turned into publicly acknowledged or patched. It labored towards Firefox variations 64 to 68. The sandbox smash out Recordsdata relied on turned into mounted in 2019.
The researchers painted a picture of an exploit market that’s more and more out of alter. They wrote:
TAG’s take a look at has confirmed the proliferation of business surveillance and the extent to which industrial spyware and adware distributors have developed capabilities that have been beforehand most engrossing out there to governments with deep pockets and technical experience. The expansion of the spyware and adware commerce places prospects at fear and makes the Web much less secure, and whereas surveillance expertise will greater than seemingly be impartial beneath nationwide or worldwide guidelines, they’re on the full vulnerable in heinous options to habits digital espionage towards a fluctuate of teams. These abuses state a excessive fear to on-line security which is why Google and TAG will proceed to have interaction movement towards, and submit take a look at about, the commercial spyware and adware commerce.
Variston joins the ranks of different exploit sellers, together with NSO Neighborhood, Hacking Personnel, Accuvant, and Candiru.

